Introduction
As the name kind of suggests, DevSecOps brings in security in to various business processes of Devops. Implementing Devsecops needs to be meticulous and requires a strong focus on security best practices. You need to unify culturally dissimilar teams of Security, Operations, Development. Also enhanced Testing to build a quality product with enhanced security.
DevSecOps Process roadmap
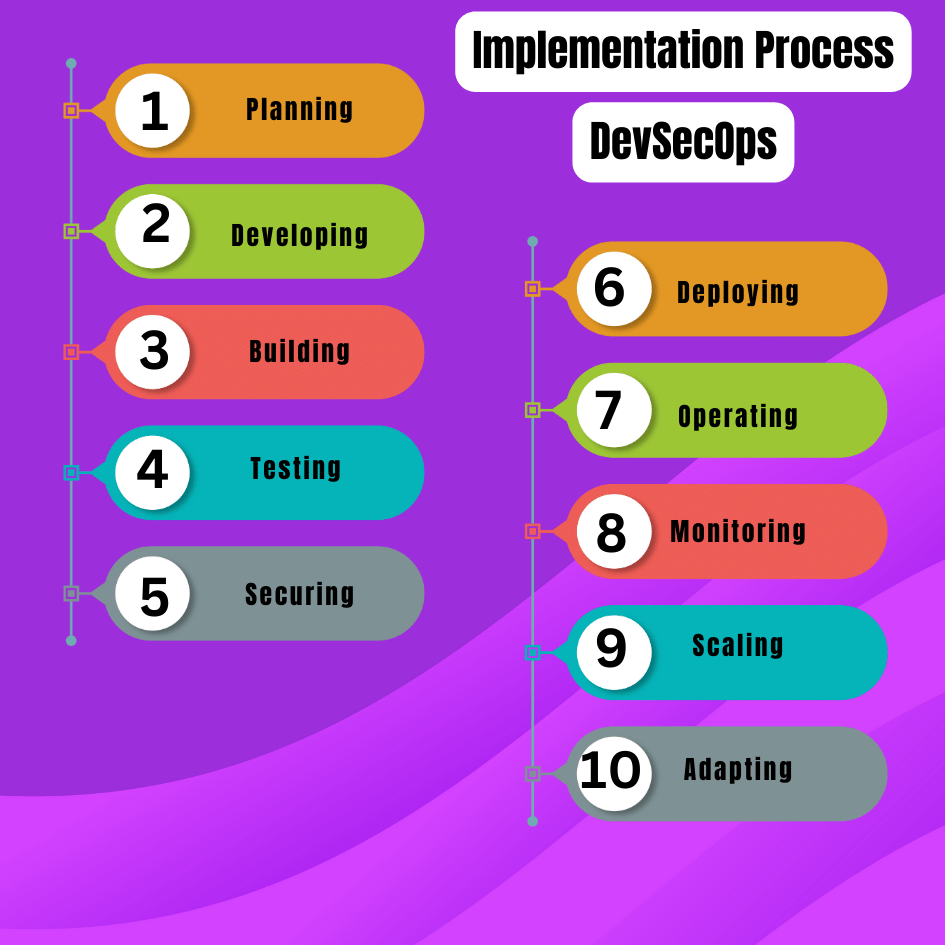
Planning
The first step in approaching any task is planning, and the core focus of DevSecOps—security—begins here. During the planning stage, DevSecOps professionals need to do more than just create feature-based descriptions. The emphasis should be on considering security and performance, defining acceptance test criteria, outlining application interfaces and functionality, and developing threat-defense models.
Developing
Developers should approach DevSecOps with a “how to do it” mindset rather than a “what to do” mindset. They need to bring together available resources for guidance, establish reliable practices, and implement a code review system for themselves and the team to follow.
Building
Automated build tools can significantly enhance the entire DevSecOps implementation process. These tools promote test-driven development, establish standards for generating release artifacts, and use statistical code analysis tools to ensure that the design aligns with the team’s coding and security standards. They can also be used to identify vulnerabilities within libraries related to the application and remediation.
Testing
Automated testing in DevSecOps utilizes strong testing practices including front-end, back-end, API, database and passive security testing.
Securing
In DevSecOps, traditional testing methods always remain in place. However, there is a tendency to identify issues toward the end of the development process. By using advanced practices such as security scanning, we become more aware of the issues and can determine whether the threat is serious or not.
Deploying
Automated provisioning and deployment can accelerate the development process and make it more consistent. Infrastructure-as-code tools can carry out auditing of properties and configurations, thereby ensuring secure configurations throughout the IT infrastructure.
Operating
The Operations team regularly monitors and upgrades systems as important tasks. DevSecOps teams deploy infrastructure-as-code tools to update and secure the entire organization’s infrastructure quickly and efficiently, eliminating the scope for human error. Operations personnel must be especially vigilant about zero-day vulnerabilities.
Monitoring
It is crucial for an organization to implement a robust continuous monitoring program with real-time capabilities to track system performance and detect any anomalies in their early stages. This proactive approach of monitoring for security irregularities can prevent breaches.
Scaling
Organizations no longer spend precious hours and money on maintaining large data centers. With virtualization solutions and the cloud, they can scale their IT infrastructure or replace it in the event of a threat, something impossible to do with a traditional data center.
Adapting
Constantly striving for improvement is essential for an organization’s growth. To achieve the desired growth, an organization must evolve its practices, including DevSecOps practices related to security, functionality, and performance. Therefore, it’s important for an organization to embrace continuous improvement and adapt to external trends.
Conclusion
In conclusion, DevSecOps embodies a proactive approach to security integration within the software development process. By merging development, security, and operations, DevSecOps promotes continuous collaboration, automation, and monitoring to enhance software security, accelerate development, and ensure a secure and agile environment for deploying applications.